Protecting a Dedibox server using CrowdSec
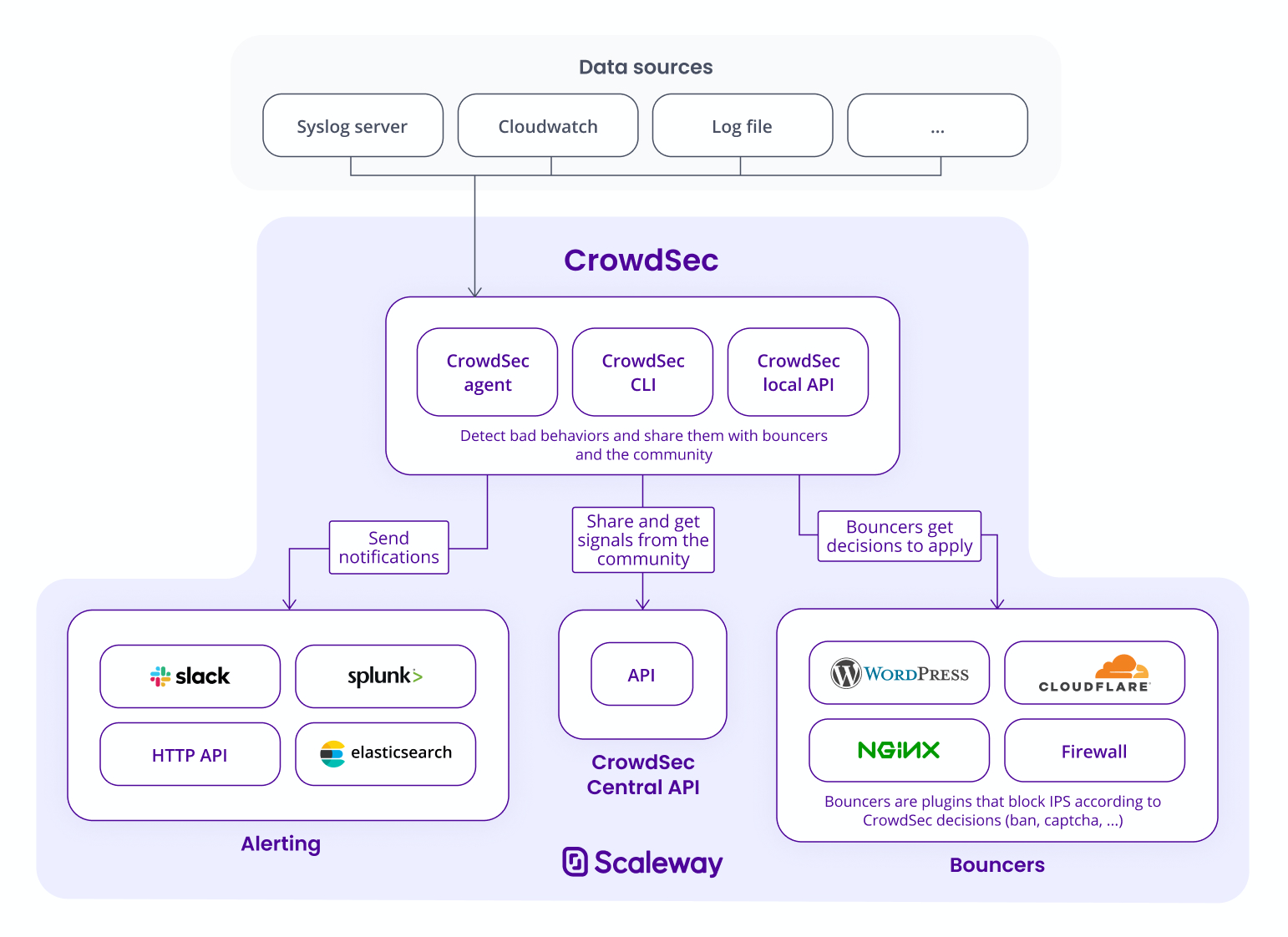
CrowdSec is an open-source software that detects malicious behavior from various connection sources, including infrastructure, systems, and applications. Similar to Fail2Ban, CrowdSec reads logs from several sources (eg: files and streams). It then parses and extracts information such as IPs, time, and environment to match it to patterns called scenarios.
Once malicious behavior is detected, its IP is stored via the Local API (LAPI), and another software called bouncer, also deployed on your machine, restricts access to this IP on your resources by querying the LAPI every X seconds. Various bouncers exist, blocking IPs with a firewall (iptables, nftables), Cloudflare, or Nginx.
Another feature enables every user of CrowdSec to share their banned IPs to a Central API (CAPI) managed by the CrowdSec team. When an IP is identified as being dangerous, it is shared with the whole community and is banned by the bouncers. This feature can be deactivated.
In this tutorial, we will set up CrowdSec on a Dedibox and protect the SSH connection.
Before you start
To complete the actions presented below, you must have:
- A Scaleway account logged into the console
- Owner status or IAM permissions allowing you to perform actions in the intended Organization
- Created a Dedibox server and installed Debian on it
- Connected to your Dedibox via SSH as
root - Installed Docker on your Dedibox
Installing CrowdSec
-
Update the
aptpackage manager and install the dependencies:apt update apt install \ apt-transport-https \ curl \ gnupg \ lsb-release -
Add the CrowdSec GPG key:
curl -L https://packagecloud.io/crowdsec/crowdsec/gpgkey | apt-key add - -
Add the address of the CrowdSec repository:
echo "deb https://packagecloud.io/crowdsec/crowdsec/debian/ $(lsb_release -cs) main" | tee /etc/apt/sources.list.d/crowdsec_crowdsec.list -
Update the sources and install CrowdSec:
apt update && apt install crowdsecCrowdSec is now installed on your Dedibox. By default, some scenarios and parsers are installed. You can list them using
cscli:cscli parsers list ------------------------------------------------------------------------------------------------------------- NAME 📦 STATUS VERSION LOCAL PATH ------------------------------------------------------------------------------------------------------------- crowdsecurity/geoip-enrich ✔️ enabled 0.2 /etc/crowdsec/parsers/s02-enrich/geoip-enrich.yaml crowdsecurity/whitelists ✔️ enabled 0.2 /etc/crowdsec/parsers/s02-enrich/whitelists.yaml crowdsecurity/dateparse-enrich ✔️ enabled 0.1 /etc/crowdsec/parsers/s02-enrich/dateparse-enrich.yaml crowdsecurity/syslog-logs ✔️ enabled 0.4 /etc/crowdsec/parsers/s00-raw/syslog-logs.yaml crowdsecurity/sshd-logs ✔️ enabled 0.9 /etc/crowdsec/parsers/s01-parse/sshd-logs.yaml -------------------------------------------------------------------------------------------------------------Some of these parsers are used to enrich the data from the malicious behaviors, with for example their localization or whitelisting. A real parser called
crowdsecurity/sshd-logsallows to parse the logs from SSHD. Let us see the scenarios:cscli scenarios list ------------------------------------------------------------------------------------------ NAME 📦 STATUS VERSION LOCAL PATH ------------------------------------------------------------------------------------------ crowdsecurity/ssh-bf ✔️ enabled 0.1 /etc/crowdsec/scenarios/ssh-bf.yaml crowdsecurity/ssh-slow-bf ✔️ enabled 0.2 /etc/crowdsec/scenarios/ssh-slow-bf.yaml ------------------------------------------------------------------------------------------Two scenarios are also installed by default. They are designed to use the data from the
sshd-logsparser. In our current setup, we can easily detect someone who is trying to connect to your machine. We can test that by spamming an SSH connection from your local machine to your Dedibox, or using software likehydra. The scenario is configured to be banned after 5 iterations from a single IP, but feel free to edit it by following the documentation.You can find your banned IPs using
cscli:cscli decisions list +------+----------+----------------+----------------------+--------+---------+----------------+--------+--------------------+----------+ | ID | SOURCE | SCOPE:VALUE | REASON | ACTION | COUNTRY | AS | EVENTS | EXPIRATION | ALERT ID | +------+----------+----------------+----------------------+--------+---------+----------------+--------+--------------------+----------+ | 4633 | crowdsec | Ip:XX.XXX.XX.X | crowdsecurity/ssh-bf | ban | FR | XXXX | 6 | 3h59m52.953123908s | 14 | +------+----------+----------------+----------------------+--------+---------+----------------+--------+--------------------+----------+If you banned your local machine on your Dedibox, do not forget to unban it before continuing this tutorial:
cscli decisions delete -i <your ip>
Installing a bouncer
In this tutorial, we will use a bouncer that can manage iptables and ipset. Once an IP is detected by the CrowdSec Agent, the bouncer will add this IP to an ipset and his connection will be automatically dropped.
-
Install the firewall bouncer:
apt install crowdsec-firewall-bouncer-iptables -
Check that your bouncer is correctly installed:
cscli bouncers list ------------------------------------------------------------------------------------------------------------------------------------------------------------------- NAME IP ADDRESS VALID LAST API PULL TYPE VERSION ------------------------------------------------------------------------------------------------------------------------------------------------------------------- FirewallBouncer-1633604730 127.0.0.1 ✔️ 2021-10-07T11:07:32Z crowdsec-firewall-bouncer v0.0.16-debian-pragmatic-ea64223d4e41c28b5d6324e82ab07625874ce507 -------------------------------------------------------------------------------------------------------------------------------------------------------------------Ban a random IP manually to test it:
cscli decisions add -i 1.2.3.4 -
Run
ipset list. You can see that the bouncer did its job and added a lot of IPs. These are the IPs from the CAPI, automatically banned. You can also easily find your manual ban:ipset list | grep "1.2.3.4" 1.2.3.4 timeout 14387
Monitoring CrowdSec
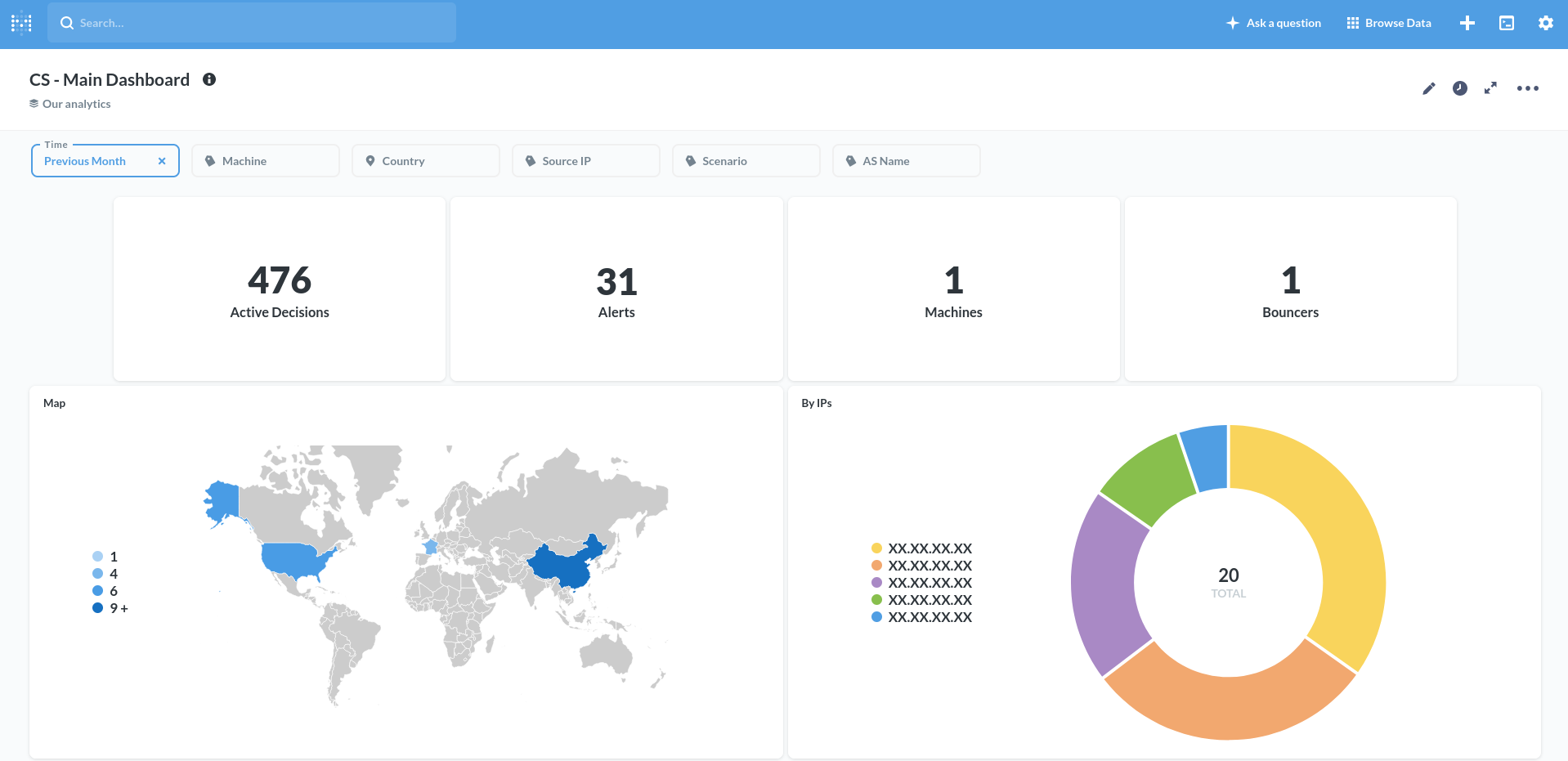
You can set up a dashboard on your machine to get a visual overview of all actions taken. However, this dashboard works only with the default database, SQLite. If you want to use PostgreSQL or MySQL, you will not be able to use the dashboard. You can start the dashboard container with:
cscli dashboard setup -l 0.0.0.0
INFO[07-10-2021 11:24:00 AM] Pulling docker image metabase/metabase:v0.37.0.2
...
INFO[07-10-2021 11:24:01 AM] creating container 'crowdsec-metabase'
INFO[07-10-2021 11:24:02 AM] waiting for metabase to be up (can take up to a minute)
...........
INFO[07-10-2021 11:24:45 AM] Metabase is ready
URL : 'http://0.0.0.0:3000'
username : 'crowdsec@crowdsec.net'
password : 'random password'You can navigate to http://<your-Dedibox-public-IP>:3000/ and log in with the credentials given. You can list all the decisions and get graphs:
Conclusion
In this tutorial, we saw how to easily set up a protection against SSH brute force attacks. CrowdSec has many parsers and scenarios available on the CrowdSec Hub. You can install them with cscli. You can also configure CrowdSec and customize it as you want. For more information, refer to the official documentation.
We saw here how to protect only one machine, but you could protect as many machines as you want with a centralized LAPI and all of your banned IPs will be synchronized.
Resources
Visit our Help Center and find the answers to your most frequent questions.
Visit Help Center