VPC FAQ
Overview
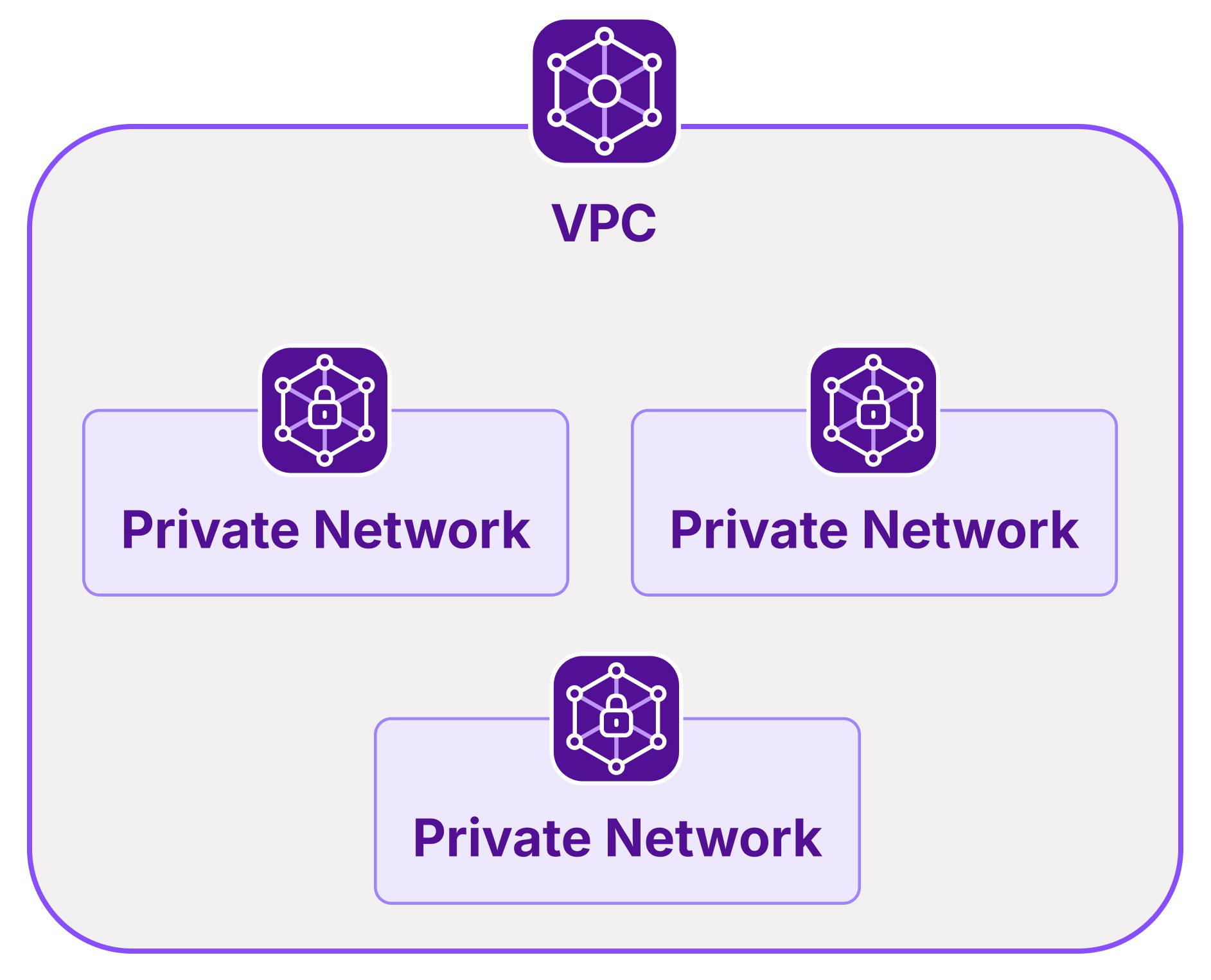
What is the difference between VPC and a Private Network?
A VPC offers layer 3 network isolation. Within each VPC, you can create multiple Private Networks (layer 2) and attach Scaleway resources to them, as long as the resources are in an AZ within the network's region. Resources attached to a Private Network can then communicate between themselves in an isolated and secure network, away from the public internet. VPC routing facilitates communication between resources on the different Private Networks within the VPC.
What is a default VPC?
If you created your Scaleway Project before 13 May 2025, one default VPC was automatically created in it for each region (Paris, Amsterdam and Warsaw). You can now opt to delete these default VPCs, if you wish.
If you created your Scaleway Project after 13 May 2025, default VPCs are no longer pre-created for the Project.
Find out more in our dedicated documentation.
What are Private Networks?
Layer 2 Private Networks sit inside layer 3 VPCs. Private Networks are a managed cloud service allowing you to create layer 2 ethernet-switched domains.
These domains can also be called virtual LAN (VLAN). They are virtual but completely private local networks that securely connect your Scaleway resources without necessarily exposing them publicly. Scaleway resources including Instances, Elastic Metal servers, Load Balancers, and Databases are all compatible with Private Networks.
What is IPAM?
IP Address Manager (IPAM) is Scaleway’s tool for planning, tracking, and managing the IP address space of Scaleway products. It acts as a single source of truth for the IP addresses of Scaleway resources, and has a number of associated functionalities to help manage your Scaleway IPs, such as the ability to reserve an IP on a Private Network and attach it to a specific resource. See our IPAM FAQ for more details.
How are NACLs different from security groups?
Security groups filter public traffic on your Instances, whereas NACLs filter traffic to/from Private Networks only.
Offering and availability
What happened to my classic, mono-AZ Private Network?
When VPC and regional Private Networks moved from Public Beta to General Availability, all mono-AZ Private Networks were automatically migrated to be regional. Read the documentation to find out more about the migration process.
Pricing and billing
How much does it cost to create a VPC, Private Network, or reserved private IP address?
The following resources and features are free of charge:
- VPCs and VPC routing
- Private Networks (except for Elastic Metal servers and Apple silicon)
- Reserved private IP addresses on IPAM
Specifications
Do resources in a Private Network require a public IPv4 address?
No, they do not require a public IPv4 address.
Do I have to restart a Scaleway resource after adding Private Networks?
No, Private Network interfaces will appear on your resources without any reboot.
Can resources in a Private Network access the internet without a public IPv4 address?
Yes. You can attach a Public Gateway to your Private Network to provide internet access to your Instances, Elastic Metal servers, and other attached Scaleway resources.
Do non-IP protocols work over Private Networks?
Technically, any Ethernet payload should work over Private Networks. However, only IPv4 and IPv6 are officially supported. If you have real use cases for other protocols, let us know by reaching us on the Scaleway Community Slack.
Quotas and limitations
Can I connect multiple Private Networks to the same Scaleway resource?
This depends on the type of resource. For Instances and most other products, you can configure up to 8 Private Networks on the same Scaleway resource. Some resource types, such as Managed Databases and Serverless Functions and Containers, only support one Private Network attachment per resource. Refer to the product's documentation on Private Networks, or Getting the most from Private Networks for more information.
How many resources can I attach to each Private Network?
A maximum of 512 resources can be attached to each Private Network. Note that for Elastic Metal servers and Apple silicon Mac minis, only 250 of these resource types can be attached to a single Private Network.
The size of your Private Network's subnet (defined via its CIDR block) does not impact the number of resources you can attach. Regardless of the subnet mask, the number of attachable resources is governed by a fixed platform limit.
Bear in mind only that creating too small a subnet will limit the number of available IP addresses in the Private Network. The default subnet mask of /22 for IPv4 gives you far more available IP addresses than the attachable resource limit.
What other quotas are enforced for the VPC product?
See our dedicated quotas page for full details.
Does a resource's advertised bandwidth limit apply to public connections only, or also to Private Networks?
This limit applies per network connection. For example, an Instance offer with a bandwidth of 500 Mbps, gets 500 Mbps to the internet, and 500 Mbps to each Private Network.
Compatibility and integration
Are Serverless Containers compatible with VPC routing?
Yes, Serverless Containers are compatible with VPC routing.
Are Serverless Functions compatible with VPC routing?
No, Serverless Functions are not currently compatible with VPC routing.
Do Private Networks support IPv6?
Yes, when you create a Private Network, both an IPv4 and an IPv6 CIDR block are defined. The IPv6 CIDR block is defined automatically and "invisibly" by default at the time of creating the Private Network. It cannot be modified either at the time of creation, or afterward.
It is a /64 block, guaranteed to be unique within the VPC and not overlapping with any of your other Private Networks. Resources that support private IPv6 addressing, e.g. Instances, can then acquire an IPv6 address when they join the Private Network.
Do Private Networks support IP autoconfiguration?
Yes, DHCP is an inbuilt function of Private Networks and provides IP autoconfiguration for your attached resources. Alternatively, you can use Scaleway IPAM to reserve specific IP addresses on a Private Network and use these to attach resources.
Usage and management
Can I route traffic between different Private Networks on the same VPC?
Yes, VPC routing allows you to automize the routing of traffic between resources in different Private Networks within the same VPC.
Can I route traffic between different Private Networks in different VPCs or different Scaleway Projects?
This is not currently possible. You may consider using a VPN tunnel to achieve this, for example IPsec or WireGuard. Scaleway also offers an OpenVPN InstantApp, making it easy to install a VPN directly on an Instance.
Can I control traffic flow between my VPC's Private Networks?
Yes, use the Network ACL feature to filter packets flowing between the different Private Networks of your VPC. By default, all traffic is allowed to pass, until you start to add rules to the VPC's NACL.
How can I attach my VMs on a Proxmox cluster on Elastic Metal to a Private Network?
For this purpose, use the option of attaching a custom resource to a Private Network, specifying its MAC address. Full instructions for attaching custom resources are in the Private Networks documentation.
You can also reserve a private IP address with IPAM, and use this reserved address to attach a custom resource.
Do resources' IP addresses on a Private Network risk changing when allocated by managed DHCP?
With Private Networks' inbuilt managed DHCP, a private IP is allocated when the resource is attached to a Private Network, and released only when the resource is detached or deleted. The IP address remains stable across reboots and long power-offs, and will not change except upon deletion or detachment from the Private Network.
Nonetheless, you can also reserve specific IPs from a Private Network's CIDR block, and use these IPs to attach specific resources, if you prefer. See our documentation on how to reserve IPs.
Support and troubleshooting
Why can I not route traffic to my Managed Database on another Private Network?
Only Managed PostgreSQL and MySQL Database Instances created after July 28th 2025 are compatible with VPC routing. Maintenance scheduled for later in August 2025 will make all pre-existing Managed PostgreSQL and MySQL Database Instances compatible as well.
Why can I not delete my Private Network even though it is empty?
You might have a reserved IP address that is blocking the deletion. Check out our troubleshooting page for guidance.